Threat Intelligence
Dangerous Invitations: Russian Threat Actor Spoofs European Security Events in Targeted Phishing AttacksDecember 4, 2025

Threat Intelligence
Dangerous Invitations: Russian Threat Actor Spoofs European Security Events in Targeted Phishing AttacksDecember 4, 2025

Threat Intelligence
APT Meets GPT: Targeted Operations with Untamed LLMsOctober 8, 2025
Threat Intelligence
Go Get ‘Em: Updates to Volexity Golang ToolingAugust 11, 2025
Threat Intelligence
Phishing for Codes: Russian Threat Actors Target Microsoft 365 OAuth WorkflowsApril 22, 2025

Threat Intelligence
GoResolver: Using Control-flow Graph Similarity to Deobfuscate Golang Binaries, AutomaticallyApril 1, 2025

Threat Intelligence
Multiple Russian Threat Actors Targeting Microsoft Device Code AuthenticationFebruary 13, 2025

Threat Intelligence
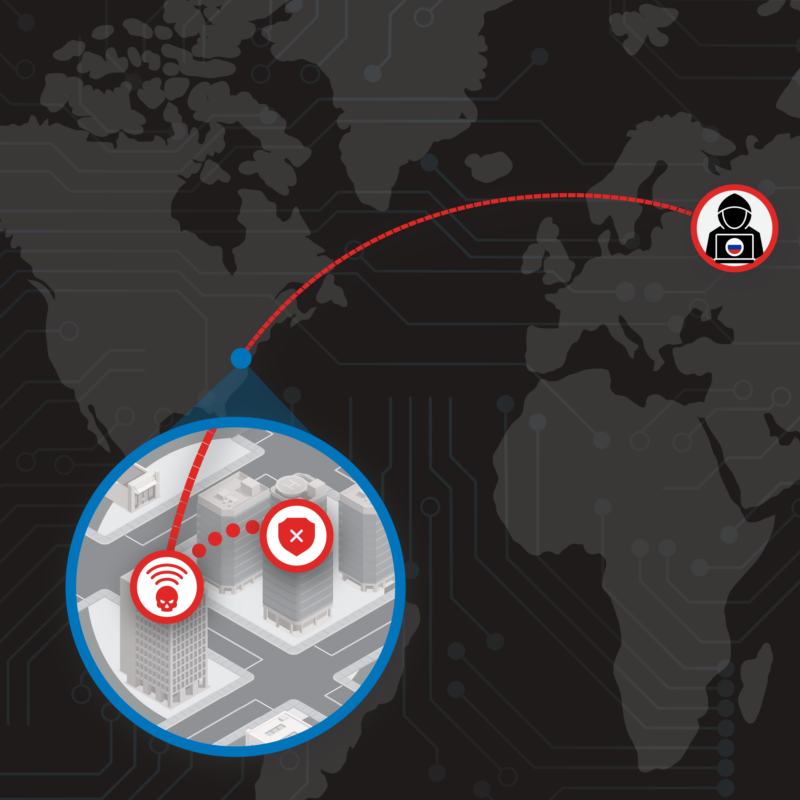
The Nearest Neighbor Attack: How A Russian APT Weaponized Nearby Wi-Fi Networks for Covert AccessNovember 22, 2024
Threat Intelligence
BrazenBamboo Weaponizes FortiClient Vulnerability to Steal VPN Credentials via DEEPDATANovember 15, 2024